Ethernet is used extensively in industrial automation applications, and in the office environments of industrial firms. This leads many to believe the network security procedures used in the office can simply be applied to industrial networks. While this would make implementation easier, it’s not that simple as there are some important distinctions between security practices for industrial and office Ethernet networks.

Understanding these differences helps users protect their industrial automation networks, gives them a rationale for rejecting some corporate IT policies which don’t fit the industrial world, and provides background information for discussions with company IT personnel.
Main Threat
Office networks are primarily concerned with data security, while the biggest concern for industrial automation networks is uptime.
Office networks contain all manner of highly sensitive data such as salary, accounts payable and receivable, revenue, profit margins, customer lists and other information. This data must be guarded from network intrusion and prying eyes at all costs. Continuous uninterrupted 24/7 uptime for these networks is generally not particularly important, as service interruptions of a few minutes in most applications can be tolerated. For many corporate intranets, longer interruptions of hours or even days can often be scheduled for weekends and holidays.
Industrial automation networks typically don’t transmit data with this level of sensitivity, but unscheduled downtime is to be avoided, and in many cases scheduled downtime is only available infrequently. Because uptime is so important, access if often more limited, because greater access poses more cyber security risk and possible service interruption.
Limited Access
Many office systems must have extensive connections to the outside world. Salespeople in the field need to have access to customer information, payroll systems are linked to banking systems for direct deposit, etc.
On the other hand, connections to industrial automation networks can be limited to only those who absolutely require access, and the level of access can be restricted based on each person’s requirements. With such closely regulated access, certain security measures can be implemented which wouldn’t be practical for an office network.
For example, each person granted access to the industrial automation network can be limited to only certain network areas and functions. This constrains where they’re able to interact with the network and it’s connected components. Maintenance personnel and machine operators might have full access, while plant management might have read-only access to HMIs.
Access controls are easier to implement with industrial automation as opposed to office networks because the size and stability of each is very different.
Size and Stability
Office networks tend to be very large when compared to industrial automation networks. A manufacturing company might have a handful of PCs, HMIs and controllers connected via Ethernet on the plant floor. The same company is likely to have many more PCs, tablets and smartphones in traditional IT applications connected via Ethernet, intranet and Wi-Fi networks.

Not only are office networks large, they tend to change much more frequently as employees come and go, connecting and disconnecting their PCs and other devices. Industrial automation networks are not only smaller, they are much more static. Adding another machine and its HMI or controller to a production system is generally not a frequent occurrence, and it’s not unusual for an industrial automation network to stay essentially the same for months or even years.
Communication patterns are also much more static with industrial automation networks. Sensors only talk to one controller, and the ways in which controllers communicate are routine and predictable. Any deviations from normal patterns can be detected and indicate a network problem or possible cyber intrusion.
Because changes are so infrequent, it’s possible and advisable to enforce very strict change management procedures for industrial automation networks, which enhance security at the cost of flexibility. Smaller networks also make it easier to install redundant network links, which isn’t practical or required with office networks.
Office networks tend to be segmented by departments. Accounting, sales and legal each have access to their network areas, but not to others. Industrial automation networks are similarly segmented by area, but also by levels, often as defined by the ISA 95/Purdue reference model (Figure). Level 0 represents the physical process, Level 1 is control and monitoring, and Level 2 is supervisory control.
Hardware and Software
Office networks connect PCs, tablets, printers and other off-the-shelf standard hardware. Many of these devices are equipped with Ethernet ports and communicate via Ethernet IP and other standard protocols. An item connected as a peripheral device, such as a monitor or a network printer, typically communicates via an industry standard protocol. The software running on these devices is highly standardized in terms of network communications, plug and play for many devices, and is generally upgraded constantly with patches and security fixes.
Industrial automation networks connect HMIs, controllers, motor drives and other proprietary components. Unlike office networks, there is really no plug and play connectivity. While most of these components have an Ethernet port, others at Level 0 typically communicate by simpler methods such as an analog current or voltage loop.
Devices high enough on the network to use Ethernet may use a variety of different specialized adapted Ethernet protocols for communication such as EtherNet/IP or Modbus TCP. While networks can be configured to work with these different protocols, they often act as a barrier to intruders. A hacker will be very familiar with Ethernet IP, but may not be as conversant with more specialized industrial Ethernet protocols.
Software Updates
In general, office networks and systems are constantly being automatically upgraded with the latest software updates, which keeps them current with the latest cybersecurity measures. Periodic interruptions of service often occur due to automatic updates, but this is of little concern as fixes generally occur through automatic updates to other devices.
For example, printer software may be incompatible with the latest update to a Windows printer driver, but this issue is quickly resolved as the printer manufacturer automatically updates their software to keep up with Windows.
This is not the case with industrial automation software. Even if all components and networks are supplied by one vendor, any software change must be tested before its implemented, and automatic updates should not be allowed.
And when components and networks are supplied by different vendors, there is even more reason for caution. A seemingly innocuous change to one component, such as updating the Windows operating system on a PC-based HMI, could affect its Ethernet communication with a PLC.
Because any update to an industrial automation component or network must be carefully tested before installation, many end users limit updates. This makes industrial automation networks more stable than office networks, but less current in terms of software updates, a compromise many are willing to make as it often enhances uptime.
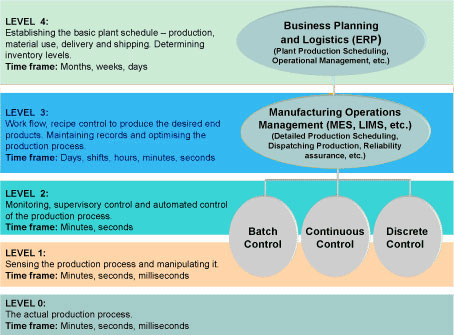
Figure, ISA 95/Purdue reference model


